RSA Security produce 2 main types of hardware
tokens. ’Standard cards’ and ’key fobs’ tokens have an LCD display that
changes every 60 seconds, but no other buttons or switches. ’Pinpad’ cards
have an LCD display, and also 0-9 keys, a diamond button and a ‘P’ button.
The way you generate your password depends on the type of token you
have.
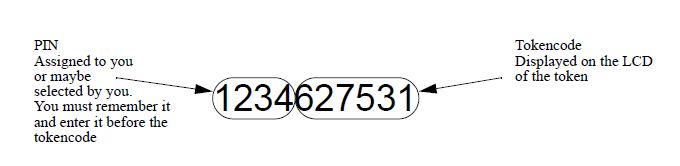
In RSA terminology, the number displayed by a token is called
the ’tokencode’ The number is typically 6 or 8 digits long and changes
every 60 seconds. The ’PIN’ is a secret 4 digit or longer number that you
will be assigned (or may have selected) and which you must remember. The
’passcode’ is what you use as your password to log in, and consists of the
PIN followed by the tokencode.
For standard tokens, the passcode is
formed from the PIN followed by the tokencode displayed on the token at
that time. So, for example, if the PIN you have remembered that was
assigned to you is ‘1234’, and the token is currently displaying the
tokencode ‘627351’, then the passcode that you will use as your password
is ‘1234627351’ (that is 10 digits). See
Figure 1. Making a password from an RSA Security Token Code (not for
Pinpads).
Figure 1. Making a password from an RSA Security Token Code (not for
Pinpads)
When a standard token is set to New PIN Mode by the ACE
administrator, you must first login in with your PIN and the current
tokencode, and you will then be prompted by Radiator for your new PIN. If
the token is set to New PIN mode and also has a Cleared PIN, you must omit
your PIN.
For Pinpad tokens, you have to enter the PIN into the
token to generate the passcode. If for example, your remembered PIN is
1234, enter the PIN into the Pinpad one digit at a time (press 1 - 2 - 3 -
4), then press the diamond button. The token will then display a new
tokencode, say ‘736284’. You would then use 736284 (that’s only 6 digits)
as your password. When a Pinpad token is set to New Pin Mode by the ACE
administrator, you must create your passcode in the usual way and then the
system will prompt them for their new PIN., When a Pinpad is in New Pin
Mode and also has a cleared PIN, the user must enter the tokencode showing
on the token (without using a PIN) first, and then the system will prompt
them for their new PIN.
Note that some types of tokens display an 8
digit tokencode, rather than a 6 digit tokencode. AuthBy ACE understands
the following parameters as well as those described in
Section 3.32. <AuthBy xxxxxx>.